This Is Bad: Heartbleed Attack Targets VPN Service
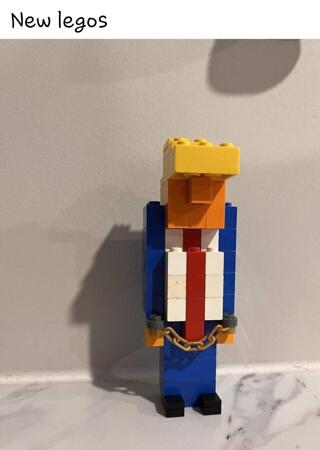
 Image via snoopsmaus
Image via snoopsmausMost of the coverage of the Heartbleed bug has focused on the security problems for websites, but there’s another avenue of attack now being exploited by hackers: the Virtual Private Network (VPN) systems used by many large and small businesses.
Security firm Mandiant reports that it is has observed a Heartbleed attack occurring “in the wild.” The attack targeted a Virtual Private Network service at an unnamed organization, gaining access to its internal corporate network — and it shows that hackers are finding the parts of the internet are least likely to have been updated to protect against Heartbleed.
The attack worked like this. When a user logs into a VPN service, it issues a “session token,” a temporary credential that is supposed to prove that a user has already been authenticated. By stealing the authentication token from the server’s memory, the attacker can impersonate the legitimate user and hijack her connection to the server, gaining access to the organization’s internal network.
This disastrous security hole in OpenSSL may have more effect on these kinds of semi-closed systems than on easily upgraded web servers, because the people who use VPNs and other types of networking applications and devices may not even realize they’re relying on the buggy versions of OpenSSL, and it may be difficult (or even impossible in some cases) to update the software.
But web servers are still a big problem as well; the Washington Post’s Brian Fung points out that we may be seeing some large scale disruptions of the Internet in the not too distant future: Heartbleed Is About to Get Worse, and It Will Slow the Internet to a Crawl.
Estimates of the severity of the bug’s damage have mounted almost daily since researchers announced the discovery of Heartbleed last week. What initially seemed like an inconvenient matter of changing passwords for protection now appears much more serious. New revelations suggest that skilled hackers can use the bug to create fake Web sites that mimic legitimate ones to trick consumers into handing over valuable personal information.
The sheer scale of the work required to fix this aspect of the bug — which makes it possible to steal the “security certificates” that verify that a Web site is authentic — could overwhelm the systems designed to keep the Internet trustworthy.
“Imagine if we found out all at once that all the doors everybody uses are all vulnerable — they can all get broken into,” said Jason Healey, a cybersecurity scholar at the Washington-based Atlantic Council. “The kinds of bad things it enables is largely limited only by the imagination of the bad guys.”
Please note! We got out in front of the rush to revoke/reissue our SSL certificates right away, the day the bug was announced, so Little Green Footballs is not vulnerable to the problem described in the Washington Post article.